The 3 Most Common Cloud Admin Oversights
 If you use Google Workspace or Microsoft 365, managing your services requires time and effort. Failing to do so can lead to wasted money and security risks. Here are the three most common cloud admin oversights we encounter.
If you use Google Workspace or Microsoft 365, managing your services requires time and effort. Failing to do so can lead to wasted money and security risks. Here are the three most common cloud admin oversights we encounter.
1 – Data and Account Retention Policies
Every business has some degree of employee turnover. Whether you are hiring replacements, reducing staff, or growing, having data and account retention policies will guide how you handle user accounts and data when an employee leaves. Without such policies, we tend to keep accounts active “in case we need some of their files or emails,” long after the need has passed.
Data and account retention policies can be both effective and simple. Here are some key elements for simple data and account retention policies:
- Determine how long you need to keep an employee’s data accessible for legal or regulatory reasons. The length will depend on your business and the user’s job function.
Outside of legal and regulatory requirements, think about:
- When should you transfer emails, files, or other content to another person.
- How long to keep an account active in the system.
- How long to keep an archive or the user’s account in the system.
- How long to keep a copy of the user’s data in your backup/recovery system.
- If you choose to export the data, how long to keep the export.
- When to delete the account after it becomes inactive, allowing you to reuse the license.
Since archive and backup/recovery solutions allow you to restore data to a different user, they offer a more cost-effective option than keeping an account active and licensed. They also help meet your legal retention requirements without the expense of an active user license.
2 – License Management
Sometimes we overlook simple actions that can save us time and money. Both Microsoft and Google allow you to add users at any time during your annual contract term. These additions become part of your contracted commitment, which you cannot reduce until renewal.
Too often, when a new employee or contractor joins the team, we immediately add a license and set them up to work. By not checking for available licenses or user accounts that can be deleted, we miss opportunities to reuse existing licenses. Consequently, we end up paying more without any added benefit.
If you have data and account retention policies, you can safely determine if and when to remove a former employee’s account. This allows you to reuse licenses and avoid incremental costs.
While the process may take a few minutes, it is simple and effective in saving money. We have seen businesses with seasonal employee turnover accumulate 25% to 50% more licenses than they actually need.
3 – On-Boarding / Off-Boarding
Small and midsize businesses may not see the need for formal on/off-boarding processes. However, not having them in place can lead to wasted time and potential security risks. Simple, efficient checklists can save you time, effort, and money
On-Boarding
The key to efficient on-boarding is knowing which applications, tools, and data the new employee should be able to access and use.
Create a simple checklist of applications, tools, and file shares. When on-boarding a new employee, determine what access is needed and check off each item as it is provided. This ensures new staff members only gain access to the resources they need.
Creating standard checklists for specific departments and jobs ensures consistent access and permissions across teams.
As a best practice, create security groups for departments and/or job functions to which you assign permissions are access rights. When on-boarding, adding new employees to the appropriate groups streamlines the process and saves time.
Off-Boarding
One of the most common mistakes made during employee departures is leaving accounts active with continued access to systems and data. This poses a security risk and can create confusion for remaining staff.
Having data and account retention policies helps ensure that past employee accounts, also known as “ghost accounts,” are removed from your systems. Creating off-boarding checklists helps ensure that application and data access gets transferred, as appropriate, to other users. Using security groups further simplifies the off-boarding process.
Your Next Step
With time-saving best practice, cloud admin services, Cumulus Global co-manages and remotely administers your IT services to save you time and money, improve productivity, enhance security, and protect your business.
Contact us about our Managed Cloud Services or schedule a no-obligation meeting with a Cloud Advisor today.
Contact us or schedule a no-obligation meeting with a Cloud Advisor today.
About the Author
 Allen Falcon is the co-founder and CEO of Cumulus Global. Allen co-founded Cumulus Global in 2006 to offer small businesses enterprise-grade email security and compliance using emerging cloud solutions. He has led the company’s growth into a managed cloud service provider with over 1,000 customers throughout North America. Starting his first business at age 12, Allen is a serial entrepreneur. He has launched strategic IT consulting, software, and service companies. An advocate for small and midsize businesses, Allen served on the board of the former Smaller Business Association of New England, local economic development committees, and industry advisory boards.
Allen Falcon is the co-founder and CEO of Cumulus Global. Allen co-founded Cumulus Global in 2006 to offer small businesses enterprise-grade email security and compliance using emerging cloud solutions. He has led the company’s growth into a managed cloud service provider with over 1,000 customers throughout North America. Starting his first business at age 12, Allen is a serial entrepreneur. He has launched strategic IT consulting, software, and service companies. An advocate for small and midsize businesses, Allen served on the board of the former Smaller Business Association of New England, local economic development committees, and industry advisory boards.

 The current United States administration continues to issue and execute dramatic changes in US policies and programs. For businesses, tariffs and their potential impact on the economy and various business sectors gets most of the media attention. Getting less attention, US Cybersecurity Policy changes will have an immediate and potentially devastating impact on many businesses and individuals.
The current United States administration continues to issue and execute dramatic changes in US policies and programs. For businesses, tariffs and their potential impact on the economy and various business sectors gets most of the media attention. Getting less attention, US Cybersecurity Policy changes will have an immediate and potentially devastating impact on many businesses and individuals. 





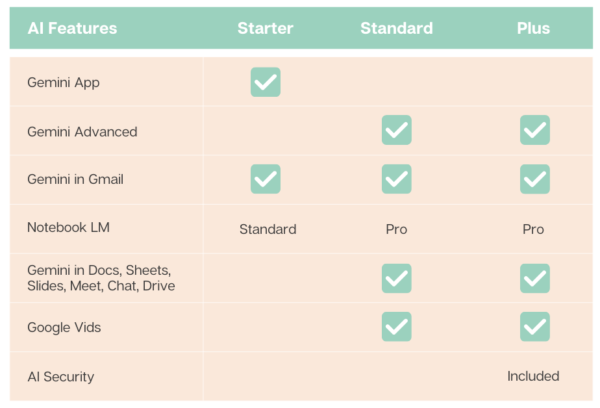
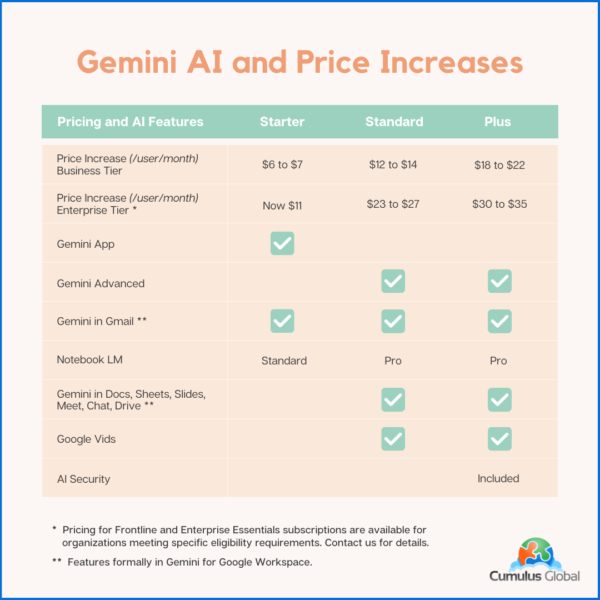
 To meet widely varying customer needs, Google offers five core subscription options spread over two tiers. For larger organizations with frontline and deskless information workers, Google offers additional, specialized license options.
To meet widely varying customer needs, Google offers five core subscription options spread over two tiers. For larger organizations with frontline and deskless information workers, Google offers additional, specialized license options.