Email Cybersecurity Risks: 3 Things to Know
As we have shared in the past, cyber attacks constantly change and evolve. We face new attack vectors, or methods, and old methods reappear. Email remains the most common starting place for cyber attacks. These attacks may be direct, or they may be the first step of a larger attack.
Over the last few months, we have seen an increase in new and reappearing email-based cyber attacks. Here are three types of attacks that you may be unaware of, but should protect against.
1 Email Burst Attack.
As the name implies, an Email Burst Attack begins when the attackers send a burst of legitimate-looking, identical emails. To the victim, the attack appears to be a technical issue, as they may receive anywhere from 10 to more than 100 emails within 20 to 90 seconds. The attack continues with a phone call or email impersonating an IT employee or a vendor. The victim is asked to “reset” a password or download software to “fix the problem,” giving the attackers access to credentials and/or the computer.
Email Burst Attacks are difficult to detect and can result in significant breaches and loss.
2 An Old-School Cyber Attack Returns
An email-based cyber attack that uses Google Groups is back after several years in the shadows. In this attack, the cyber attacker creates a Google Group, directly adds members, and sends emails to the group members. These emails range from basic spam to sophisticated phishing attacks.
The emails look legitimate because the email is from the Google Groups service, a trusted sender. As such, a Google Group attack is difficult to identify and defend against.
3 Visual Risks On The Rise
Email-based cyber attacks often use images and “calls to actions” that appear to be from a trusted source or brand.
Attackers will use images of, or from, legitimate websites to mimic the look and feel of stores, banks, and other trusted businesses. To detect these attacks, you need to compare the image and branding with the email header and meta data. This type of scanning is beyond the ability of most email threat protection services.
QR Codes pose a similar risk. In order to validate that a QR Code is safe, you need to scan the image and test the underlying URL. Because QR Codes are not a “link click”, most email scanners cannot validate they are safe.
Protecting Yourself
The newest generation of email threat protection services include the abilities to detect and mitigate these attacks. These services include:
- Detecting and blocking email burst attacks
- Letting administrators and users manage graymail, so that Google Group and similar attacks can be identified and blocked
- Scanning emails using AI-empowered computer vision to verify branding and safely test QR codes.
Cumulus Global offers email threat protection services with these capabilities within our Managed Cloud Services and as a stand-alone service offering.
Your Next Step
Get more information and assess your email threat protection services, or schedule a no-obligation meeting with one of our Cloud Advisors.
About the Author
 Christopher Caldwell is the COO and a co-founder of Cumulus Global. Chris is a successful Information Services executive with 40 years experience in information services operations, application development, management, and leadership. As COO, Chris overseas our Service Team, providing expert consulting, cloud migration, education, and support services.
Christopher Caldwell is the COO and a co-founder of Cumulus Global. Chris is a successful Information Services executive with 40 years experience in information services operations, application development, management, and leadership. As COO, Chris overseas our Service Team, providing expert consulting, cloud migration, education, and support services.



 Allen Falcon is the co-founder and CEO of Cumulus Global. Allen co-founded Cumulus Global in 2006 to offer small businesses enterprise-grade email security and compliance using emerging cloud solutions. He has led the company’s growth into a managed cloud service provider with over 1,000 customers throughout North America. Starting his first business at age 12, Allen is a serial entrepreneur. He has launched strategic IT consulting, software, and service companies. An advocate for small and midsize businesses, Allen served on the board of the former Smaller Business Association of New England, local economic development committees, and industry advisory boards.
Allen Falcon is the co-founder and CEO of Cumulus Global. Allen co-founded Cumulus Global in 2006 to offer small businesses enterprise-grade email security and compliance using emerging cloud solutions. He has led the company’s growth into a managed cloud service provider with over 1,000 customers throughout North America. Starting his first business at age 12, Allen is a serial entrepreneur. He has launched strategic IT consulting, software, and service companies. An advocate for small and midsize businesses, Allen served on the board of the former Smaller Business Association of New England, local economic development committees, and industry advisory boards. On January 15, 2025, Google announced a major shift for Google Workspace. Going forward, all Google Workspace licenses will include Gemini AI features and functions. Specific capabilities will vary by license type.
On January 15, 2025, Google announced a major shift for Google Workspace. Going forward, all Google Workspace licenses will include Gemini AI features and functions. Specific capabilities will vary by license type. 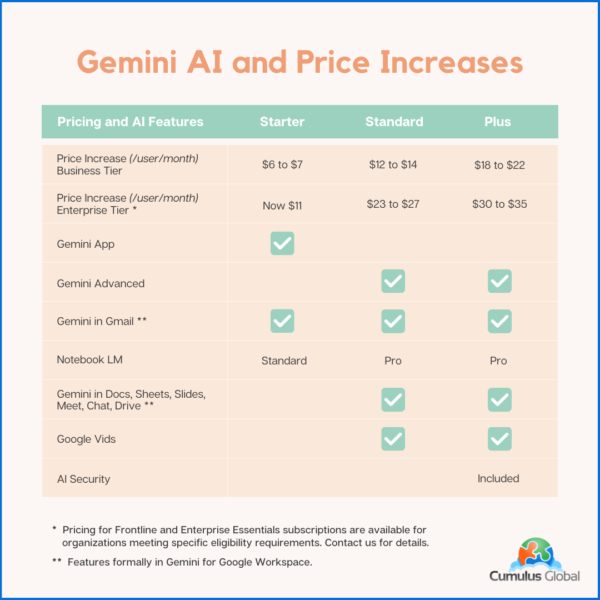
 As we head into the new year, we face an uncertain business landscape. Politics, the economy, and technology advances create new tech-related challenges and opportunities. As you make your plans, be ready for these 3 things in 2025.
As we head into the new year, we face an uncertain business landscape. Politics, the economy, and technology advances create new tech-related challenges and opportunities. As you make your plans, be ready for these 3 things in 2025.
