
Your small business depends on your IT services to run effectively and efficiently. Even so, like many small business leaders, you likely have one or more “IT Blind Spots”. The blind spots are not “all or nothing.” They evolve from decisions about what IT services are needed, wanted, and worthy of spending on at a particular point in time. Over time, internal and external factors change. If we do not take a fresh look, our IT services will not keep up.
While not intentional, these blind spots create unnecessary risks and expenses. Here are the seven (7) blind spots we see the most.
1Security and Privacy
As small business owners and leaders, we understand the need for security – especially in today’s environment. We wonder, however, how much security is enough and what we should prioritize. We see small businesses with antivirus protection on their computers, strong passwords, and basic backup/recovery. While these services were the benchmark for basic security, they are now insufficient.
Check your IT blind spots for other core security services, including multi- or two-factor authentication (MFA/2FA), advanced threat protection (ATP) for email, advanced endpoint protection and response, encryption, and immutable backup/recovery services.
If you do not have these in place, your security is likely insufficient to protect your business.
2Duplicate Services
It has never been easier to sign up for new services. With a few clicks, payment information, and a quick setup, your new, cloud-based application or service is up and running. The convenience is great when you need something specific or a new solution. The low barrier to entry, however, makes it easier to sign up for apps and services that duplicate others you already have in place.
Check your IT blind spots for these duplicate services. We most often see companies paying for Zoom or GoTo, even though they have Microsoft Teams or Google Meet for online meetings and presentations. Some spend on Slack and other tools instead of using Teams or Google Chat services that are already in place. Rather than managing permissions to share files from Microsoft 365 or Google Workspace, small businesses often spend more on Dropbox and other services. While these are the most common duplicate services, we often see others across a wide range of apps and functions.
3Shadow IT
We used to define Shadow IT as any IT service in use without proper vetting or authorization. Today, we expand the definition to include consumer-grade hardware, software, and services. Team members using unauthorized IT services typically create security risks, increase costs, reduce control of company information, violate information privacy rules, and put data at risk. While less costly up-front, consumer-grade equipment, software, and services typically lack the security and integration needed for business use.
Check your IT blind spots and survey your environment for Shadow IT. Team members often go rogue for personal preference, convenience, or because they do not understand how to use features and functions already in place.
4Latent Apps and Services
When was the last time you looked to see if you were paying for IT services that you no longer use or need? With the low barrier to entry for cloud services, we often see companies that have signed up for an app or service, only to later decide that it is not the right solution or to see usage decline over time. Without a set process for on/off-boarding IT services, these often remain idle, incurring monthly or annual fees.
Check your IT blind spots for applications and services. Review company and staff personal credit cards for recurring payments. Scan Microsoft 365 and Google Workspace accounts for apps and services with federated logins.
5Business Continuity
While almost all small businesses like yours have backup/recovery in place for most of their systems and data, most still lack a business continuity solution. Even without a big disaster, the loss of a single, key system can be crippling.
Check your IT blind spots for business resilience. Can you run your business without your IT systems and services? For how long? Which systems and services can you live without for a short period of time and which are critical to your business? The answer to these questions dictates the types and extent of business continuity services you need. Focus on what you need to reasonably run your business while you make repairs and complete larger recovery efforts.
6Cyber Insurance
Most small businesses know that they should have cyber insurance in place, and many do. Too often, however, we see small businesses signing on to policies with inadequate or inappropriate coverage. We also see many businesses overpaying for cyber insurance to cover risks that could easily be reduced with incremental security services.
Check your IT blind spots for appropriate cyber insurance coverage and rates. If your policy was not purchased through a specialized agent or broker, an independent review may be worthwhile. If you do not yet have a policy, check out our resources and ask about our cyber insurance readiness assessment.
7Utilization
Multiple services tell us that most small businesses use about 15% of the capabilities in their Microsoft 365 or Google Workspace services. Your investment in Microsoft 365 or Google Workspace includes a rich set of features and functions – major and minor – that help your team collaborate and work more efficiently, individually and as a team.
Check your IT blind spots to understand how well your team is using the tools available to them. A little bit of education, training, and guidance can boost productivity within Microsoft 365 and Google Workspace by up to 60%.
Call to Action:
If you suspect, or just wonder, what is in your IT blind spot, we can help. We can help you check your blind spots and assess what, if any, changes are necessary or recommended. Once decided, we can help you plan and execute those changes. Contact us or schedule time with one of our Cloud Advisors.
About the Author
 Allen Falcon is the co-founder and CEO of Cumulus Global. Allen co-founded Cumulus Global in 2006 to offer small businesses enterprise-grade email security and compliance using emerging cloud solutions. He has led the company’s growth into a managed cloud service provider with over 1,000 customers throughout North America. Starting his first business at age 12, Allen is a serial entrepreneur. He has launched strategic IT consulting, software, and service companies. An advocate for small and midsize businesses, Allen served on the board of the former Smaller Business Association of New England, local economic development committees, and industry advisory boards.
Allen Falcon is the co-founder and CEO of Cumulus Global. Allen co-founded Cumulus Global in 2006 to offer small businesses enterprise-grade email security and compliance using emerging cloud solutions. He has led the company’s growth into a managed cloud service provider with over 1,000 customers throughout North America. Starting his first business at age 12, Allen is a serial entrepreneur. He has launched strategic IT consulting, software, and service companies. An advocate for small and midsize businesses, Allen served on the board of the former Smaller Business Association of New England, local economic development committees, and industry advisory boards.
 In January 2025, Cumulus Global expanded its sustainability program to help offset the carbon footprint of our offices and operations. In partnership with Evertreen, we fund the planting of 100 trees per month.
In January 2025, Cumulus Global expanded its sustainability program to help offset the carbon footprint of our offices and operations. In partnership with Evertreen, we fund the planting of 100 trees per month. Allen Falcon is the co-founder and CEO of Cumulus Global. Allen co-founded Cumulus Global in 2006 to offer small businesses enterprise-grade email security and compliance using emerging cloud solutions. He has led the company’s growth into a managed cloud service provider with over 1,000 customers throughout North America. Starting his first business at age 12, Allen is a serial entrepreneur. He has launched strategic IT consulting, software, and service companies. An advocate for small and midsize businesses, Allen served on the board of the former Smaller Business Association of New England, local economic development committees, and industry advisory boards.
Allen Falcon is the co-founder and CEO of Cumulus Global. Allen co-founded Cumulus Global in 2006 to offer small businesses enterprise-grade email security and compliance using emerging cloud solutions. He has led the company’s growth into a managed cloud service provider with over 1,000 customers throughout North America. Starting his first business at age 12, Allen is a serial entrepreneur. He has launched strategic IT consulting, software, and service companies. An advocate for small and midsize businesses, Allen served on the board of the former Smaller Business Association of New England, local economic development committees, and industry advisory boards.
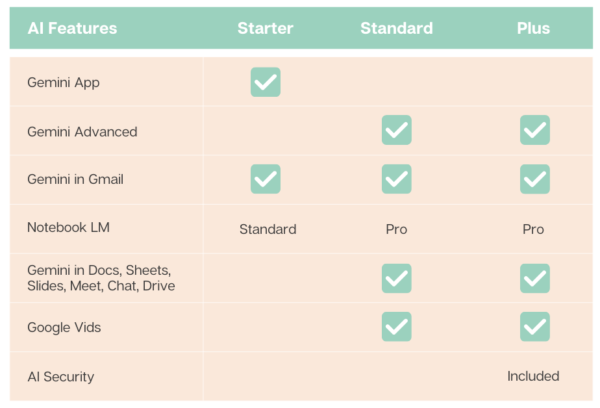
 To meet widely varying customer needs, Google offers five core subscription options spread over two tiers. For larger organizations with frontline and deskless information workers, Google offers additional, specialized license options.
To meet widely varying customer needs, Google offers five core subscription options spread over two tiers. For larger organizations with frontline and deskless information workers, Google offers additional, specialized license options. 

 In today’s fast-paced business world, the ability to maintain continuous PC operations is crucial for your business. With limited resources and manpower, you cannot afford to lose data or prolonged downtime.
In today’s fast-paced business world, the ability to maintain continuous PC operations is crucial for your business. With limited resources and manpower, you cannot afford to lose data or prolonged downtime. 





 Cyber Security Will Change Companies
Cyber Security Will Change Companies